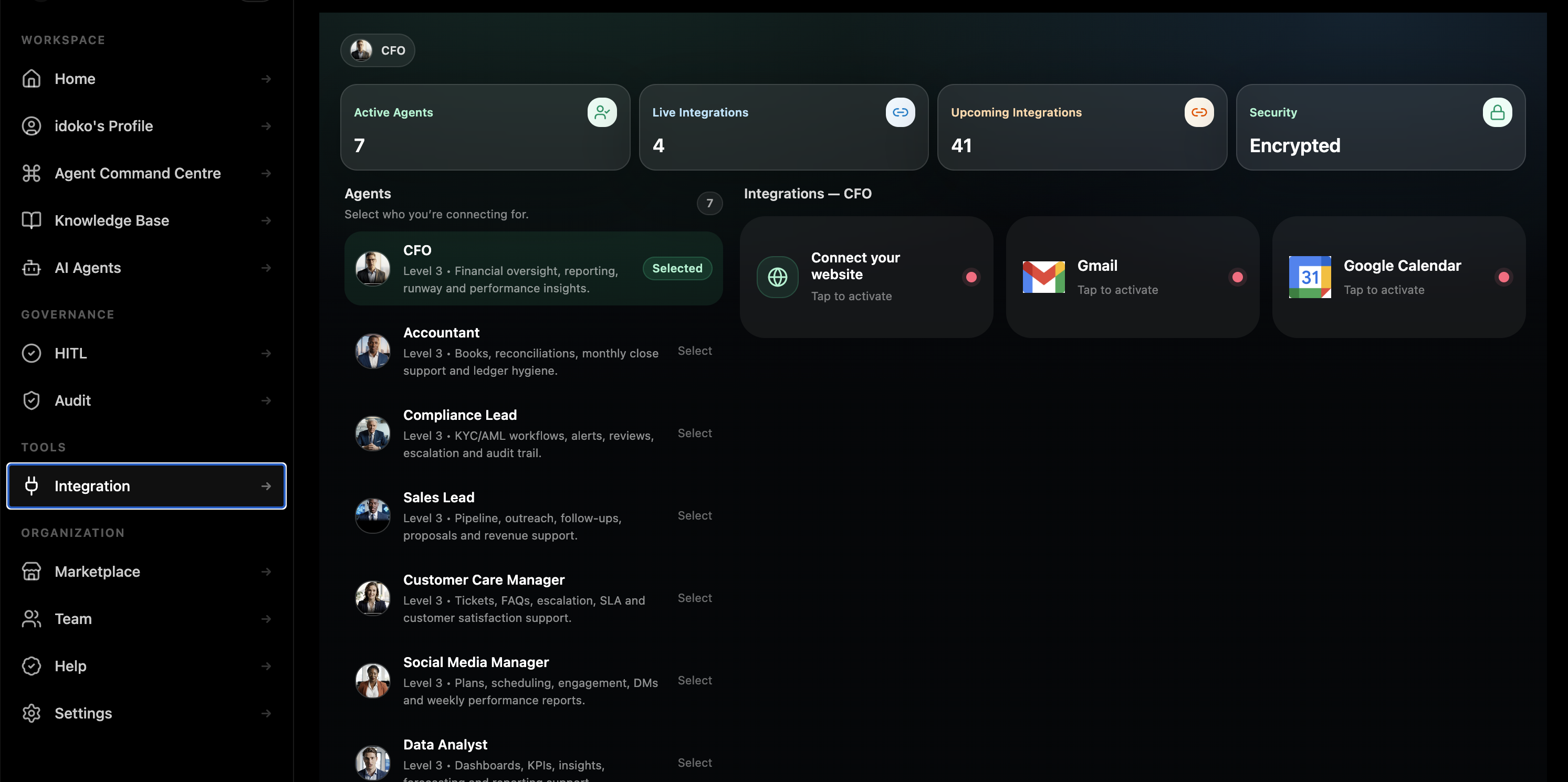
Connect Pryme to the systems your business actually runs on.
CRMs, support tools, finance, communications, identity, data warehouses, and your own APIs. Scoped credentials. Per-agent permissions. Full audit on every call.
Wherever your business already runs.
CRM & sales
Customer records, pipeline systems, and revenue workflows that agents need to read, update, and escalate.
Salesforce, HubSpot, Pipedrive, Attio, opportunity notes, outreach workflows
Customer support & success
Support desks, inboxes, escalation queues, and feedback systems that shape live service delivery.
Zendesk, Intercom, Freshdesk, Help Scout, Front, support history
Finance & banking
The systems behind payments, reconciliation, ledgers, exception review, and finance operations.
Stripe, Plaid, QuickBooks, Xero, NetSuite, reconciliation workflows
Communications
Channels where agents interact with customers and teams, including web, email, messaging, and business chat.
Slack, Microsoft Teams, Gmail, Outlook 365, WhatsApp Business, Twilio
Identity & access
Identity and directory systems that determine who can access what, and which actions require approvals.
Okta, Azure AD, Google Workspace, JumpCloud, role mapping, service accounts
Knowledge & docs
The document systems and operating knowledge bases agents learn from and reference at runtime.
Notion, Confluence, Google Drive, SharePoint, Dropbox, Box
Data & analytics
Warehouses, databases, and reporting surfaces that turn the agent from a chatbot into an operator.
Snowflake, BigQuery, Databricks, Postgres, MongoDB, Redshift, S3
Custom systems
Your internal APIs, bespoke tools, private services, and typed workflows connected through the SDK.
REST, GraphQL, gRPC, webhooks, Postgres-compatible databases, internal services
Don’t see something you need? Most teams ship a custom connector in under a day with the Pryme SDK.
Three layers between an agent and your systems.
Connect once, with your credentials. OAuth where the system supports it; scoped API keys where it does not. Credentials live in your Workspace secret store, never in transcripts and never in agent context.
Scope per agent. A given agent only sees the integrations it has been granted, and only the actions it has been granted on those integrations.
Audit every call. Every outbound call is logged with timestamp, agent, action, parameters, and result. Searchable in the audit trail and exportable when needed.
Credentials live in the Workspace secret store. Agents call tools through scoped permissions. Every call is logged before it is ever useful in production.
When the catalog ends, the SDK begins.
When you have a system that is not in the public catalog — internal database, bespoke API, vendor without OAuth — Pryme’s connector SDK lets you ship a typed connector quickly. You define the actions, auth flow, and permissions surface. Pryme handles credential storage, rate limiting, retry, and audit.
Read the connector SDK docstools.legacy_billing.lookup_invoice(invoice_id)
Your code defines what that call does. Pryme enforces the auth, the rate limit, the per-agent permission, and emits the audit event around it.
Talk to anything that speaks MCP.
If your tool stack speaks the Model Context Protocol, Pryme can treat it like any other governed tool surface. MCP-backed tools inherit the same permissions, approvals, and audit trail Pryme applies to any other integration surface.
The governance rail runs through the connector.
- An agent with Salesforce read access can read accounts but cannot update them.
- A refund inside threshold can execute directly, while a higher-value refund routes to approval first.
- An integration remains invisible to agents that have not been explicitly granted access.
Connectors that respect data boundaries.
Data residency matters. Connector traffic is designed to align with the region and tenancy boundaries defined for the Workspace rather than routing through convenience layers that break compliance assumptions.
Sensitive-data handling belongs at the connector layer too. Teams can apply redaction, minimization, and policy controls before data becomes model context.
Every connector call is part of the same immutable audit trail as the rest of the agent’s actions. Not a separate log somewhere else. The same record, the same query surface, the same governance rail.
Connect your stack. Keep your governance.
FAQ
Which integrations are live today?
The public categories on this page reflect the integration model Pryme supports today. Exact live connector availability is scoped during deployment review and expanded over time through the connector SDK.
How long does it take to add a custom integration?
Hours to a day for most internal systems through the connector SDK, depending on auth and workflow complexity.
Are credentials shared with the model?
No. Credentials live in the Workspace secret store. The model sees only the results of authorized tool calls, never the keys themselves.
Can I scope an integration to specific agents?
Yes. Per-agent grants are the default. An integration is invisible to an agent unless it has been explicitly granted access.
Do you support webhook-triggered agents?
Yes. Webhooks can be scoped per agent and event so the agent runs with the same governance and audit rules as any other trigger.
Is MCP supported?
Pryme is designed to work cleanly with MCP-style tool surfaces so that governance, permissions, and audit remain consistent even when tools come from external servers.